Blue Team Labs Online - BITS

Using BitsParser from FireEye to retrieve BITS jobs, can you help the SOC identify persistence actions conducted on a compromised host?
Incident Response
Tags: BitsParser CMD Sublime Text T1197
Scenario Using BitsParser from FireEye to retrieve BITS jobs, can you help the SOC identify persistence actions conducted on a compromised host?
Reading Material: FireEye Blog Post BitsParser GitHub Page
Environment Awareness
Evidence & Tool Discovery
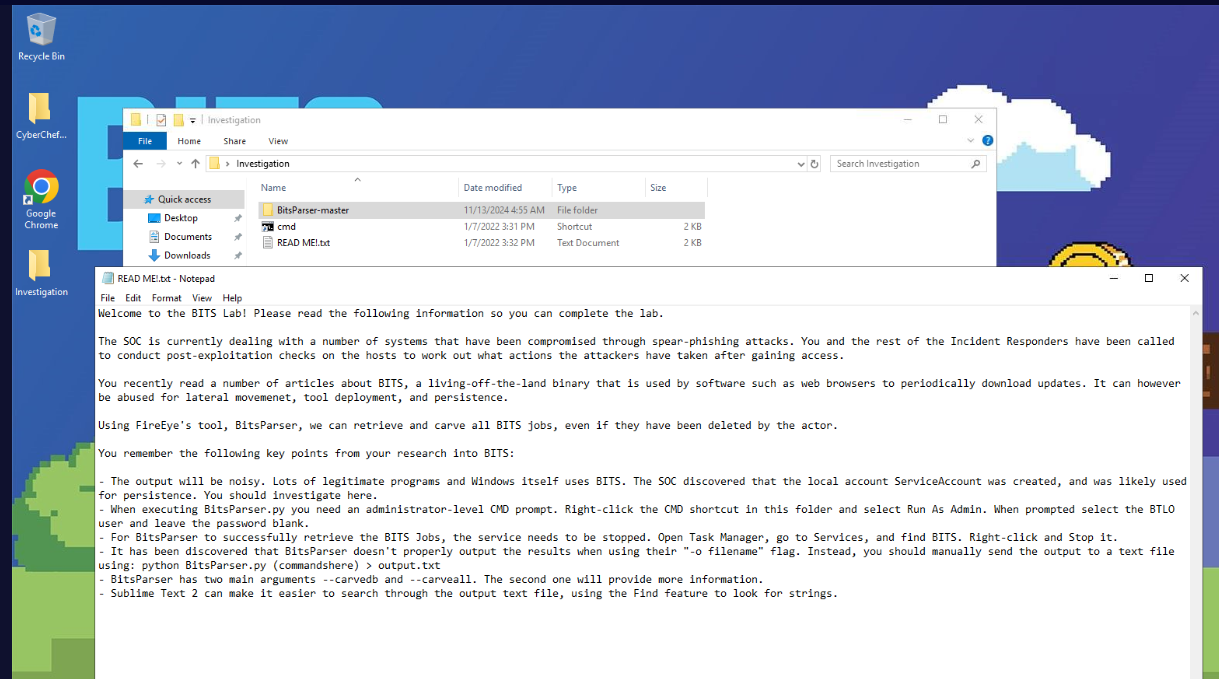
We have tool needed for this investigation ready inside Investigation folder located on the Desktop and the tool that we will have to use is BitsParser which can parse BitsAdmin artifacts from Windows system, and since there is no other artifacts provides then it mean we have to parse BitsAdmin artifacts from the investigation machine directly
Note that we also have CyberChef and Sublime text so if you are comfortable with sublime text when analyzing text/json file then you can open the output of BitsParser using sublime text
Investigation
Q1) A popular GitHub Repo for Windows privilege escalation is WinPEAS. Can you find any file downloads for winPEAS.bat in the BitsParser output? What is the associated job name? (Format: BITSJobName)
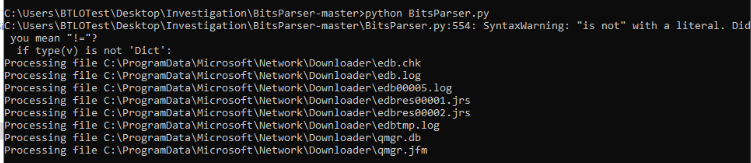
To start BitsParser, we can just simply run python BitsParser.py which will automatically parsed bitsadmin artifacts with default settings (if you have %ALLUSERSPROFILE%\Microsoft\Network\Downloader collected from other machine then you might need to use -i for that)
But look like we got a little bit of Syntax warning here
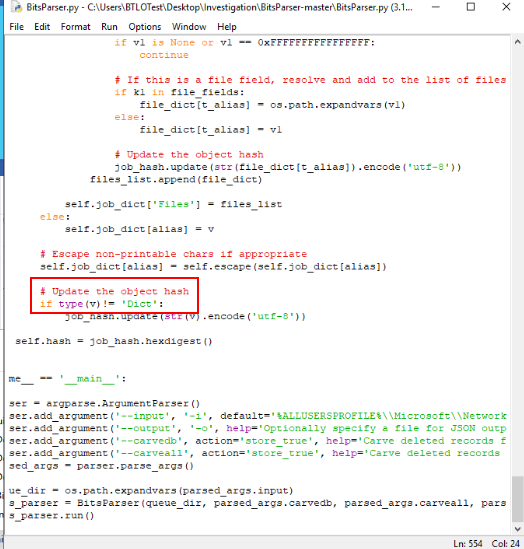
To fix this, open the script and edit this line of code from is not to !=
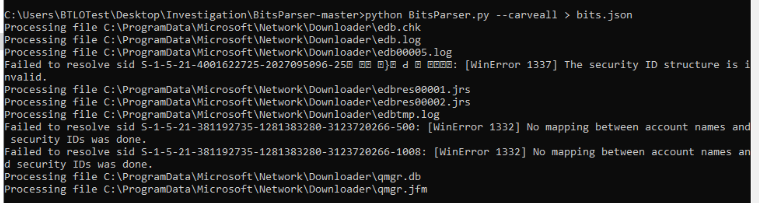
Now to carve all deleted records too then we have to use python BitsParser.py --carveall > bits.json then we should have bits.json ready to be analyzed
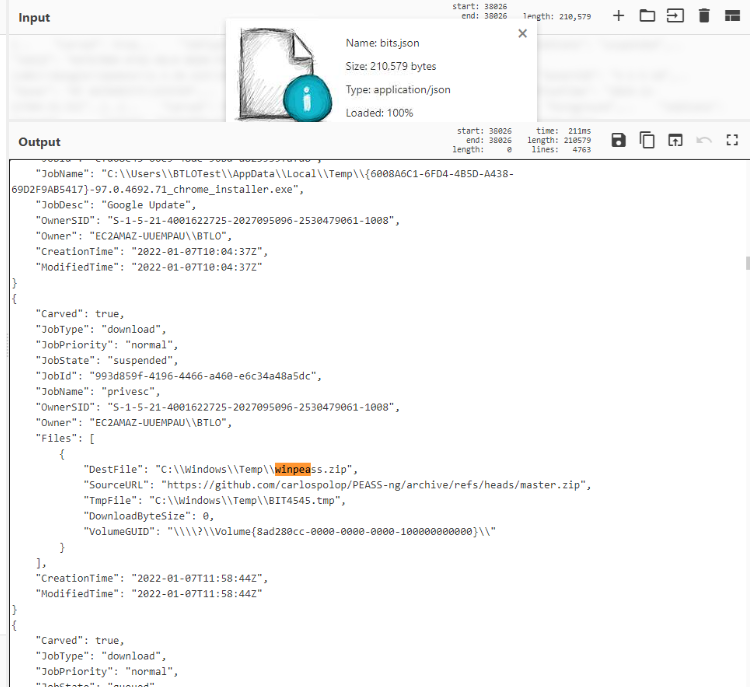
Open an output file in any text editor you preferred then search for winpeas which you can see that there are more than 1 Job that related to the string "winPEAS"
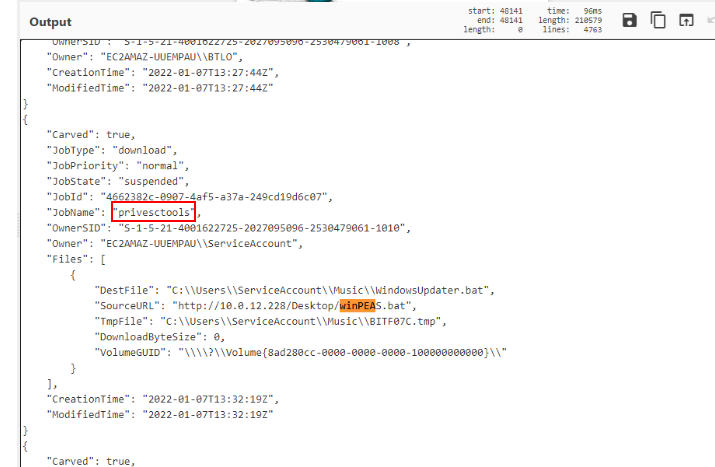
Then we can see the jobname that responsible for downloading winPEAS.bat file right here.
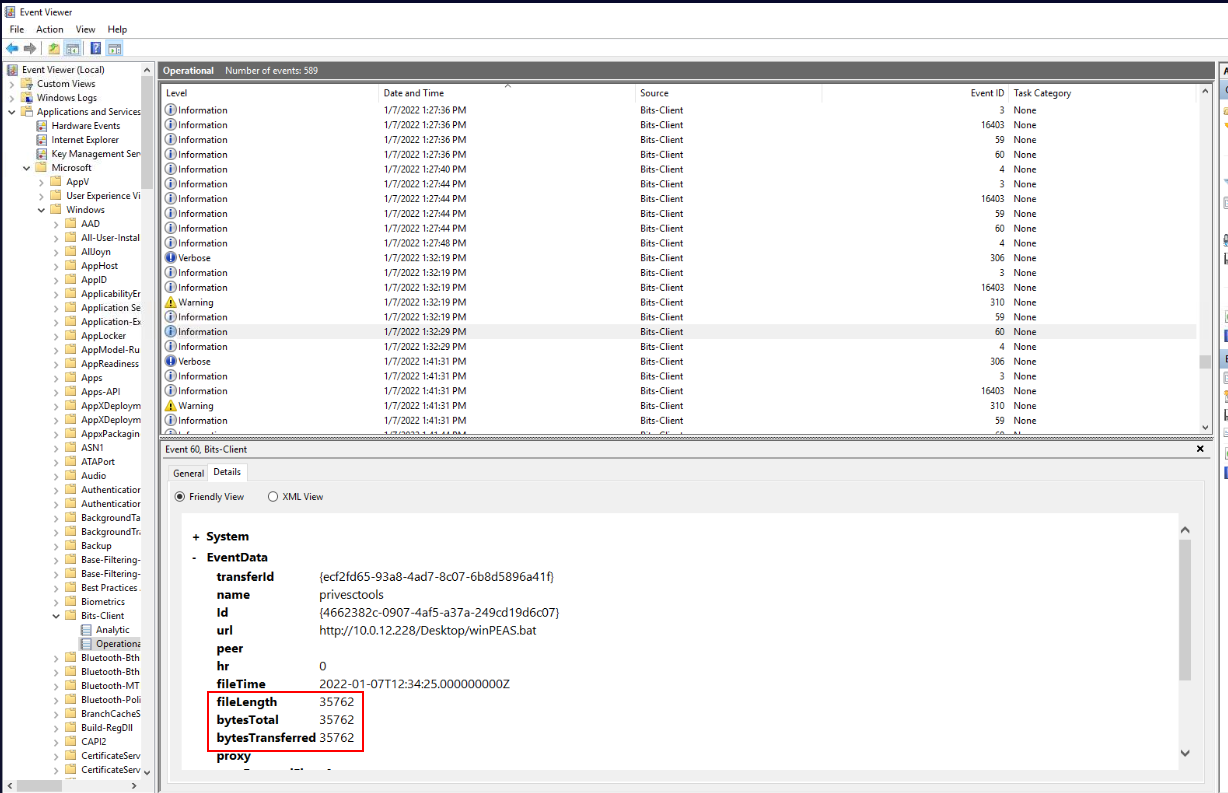
Alternatively to BitsParser, Windows also logged BitsAdmin event under "Applications and Services" -> "Microsoft" -> "Bits-Client" and we can also find the same result from this log.
Answer
privesctoolsQ2) What is the Creation Time of this job? (Format: YYYY-MM-DDTHH:MM:SSZ)
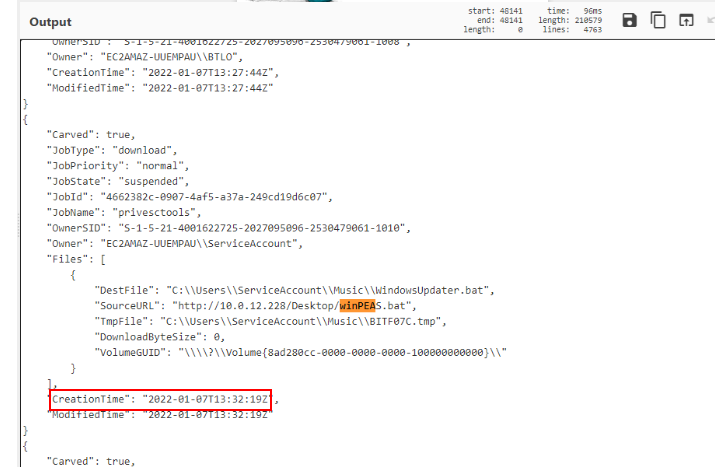
You can find the Creation time of this job right here. (its already parsed)
Answer
2022-01-07T13:32:19ZQ3) BITS can be used to download files from other systems. What is the IP address that originally hosted the file downloaded to the victim machine? (Format: X.X.X.X)
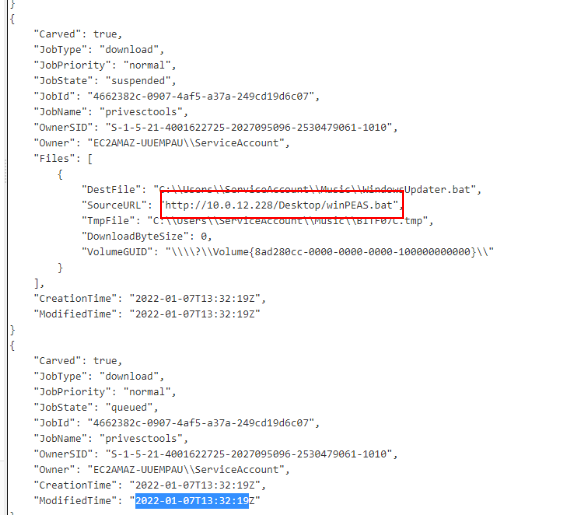
From the "SourceURL", we can see that this file was hosted from the other machine inside the internal network.
Answer
10.0.12.228Q4) What is the folder and filename used when this file was downloaded to the victim machine? (Format: \folder\file.extension)
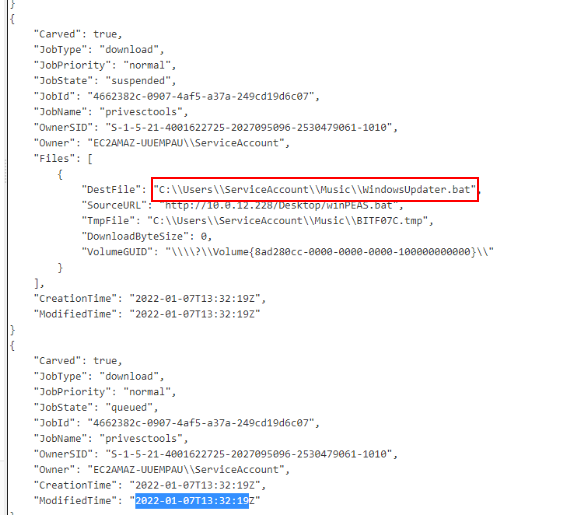
We can check "DestFile" for this which is the destination file path of this job once it successfully downloaded.
Answer
\\Music\\WindowsUpdater.batQ5) Is there any evidence of other files that include the string "winPEAS"? What is the original filename? Make sure the DownloadByteSize or TransferByteSize is greater than 0 to identify a successful download/transfer. (Format: filename.extension)
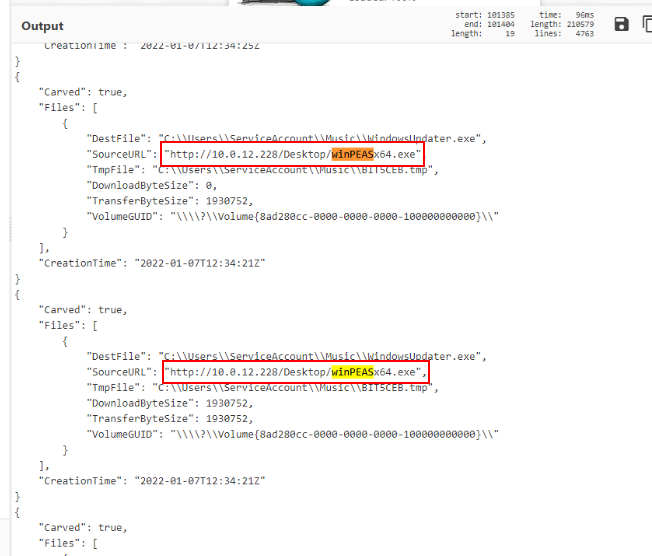
Beside bat file and zip file we just found earlier, there is also an executable file that was downloaded using BitsAdmin which is a compiled winPEAS executable for 64-bit system.
Answer
winPEASx64.exeQ6) What is the folder and filename used when this second file was downloaded to the victim machine? (Format: \folder\file.extension)
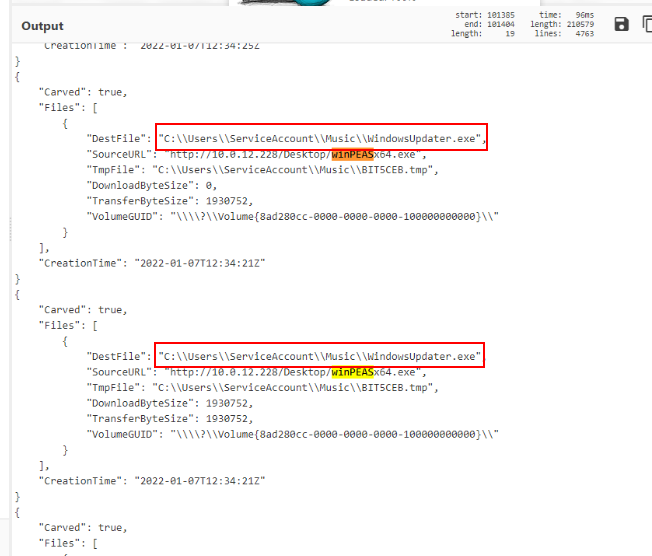
Check "DestFile" for this.
Answer
\\Music\\WindowsUpdater.exeQ7) What is the file size in bytes of this file? (Hint: Look at the DownloadByteSize or TransferByteSize)
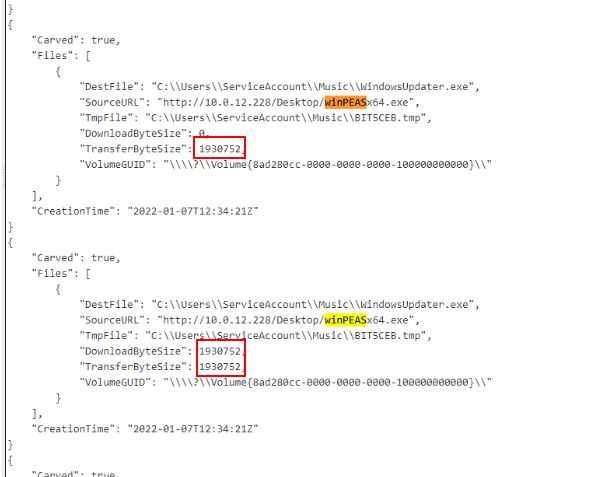
Answer
1930752Q8) The SOC saw network connections to Github in the web proxy. What is the username of the account doing this, and what is the attempted source URL? (Format: Username, https://sourceurl.tld/path)
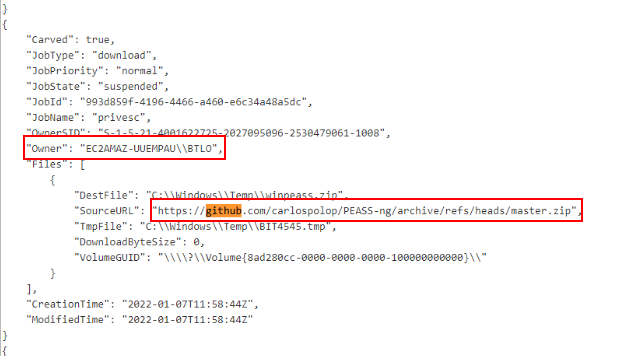
We can search for "github" string which leads us to whole PEASS-ng main branch being downloaded by BTLO user
Answer
BTLO, https://github.com/carlospolop/PEASS-ng/archive/refs/heads/master.zip https://blueteamlabs.online/achievement/share/52929/33
https://blueteamlabs.online/achievement/share/52929/33